The right network automation platform can help administrators build and maintain an organization network. Find out the top preference in the market and the benefits they offer.The current boom in network automa...
The disputes for and against outsourcing the IT services consumed by a business are several and diverse.One item to recognise is that there is no ‘one measurement fits all’ in this figure. Possibilities are tha...
The digital transformation has dramatically altered the cybersecurity expectations of healthcare offerings as the number of associated devices collapsed and network perimeters began to grow. And, this digital t...
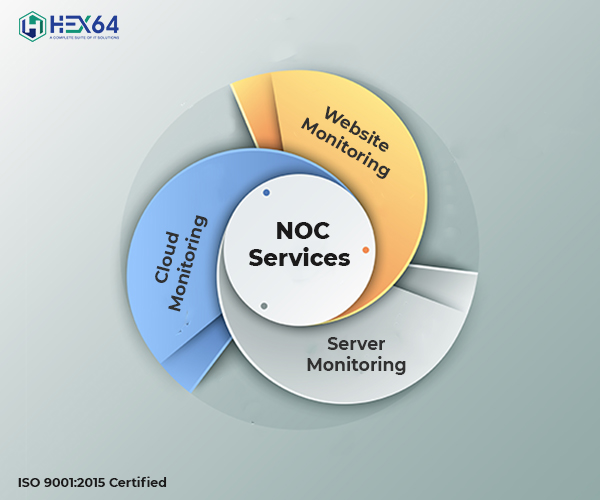
A Network Operations Center (NOC) is a place where IT specialists can support, monitor, and maintain, networks and data centers. NOC is network troubleshooting, software distribution center, router and domain n...
In today’s digital era, data is the most vital component for any business. All companies should have a data backup and recovery plan for their important data.Despite your company’s volume, data can ...
With the increasing reliance on technology, it is becoming increasingly necessary to secure every aspect of online information and data. As the Internet grows and computer networks become more important, data i...
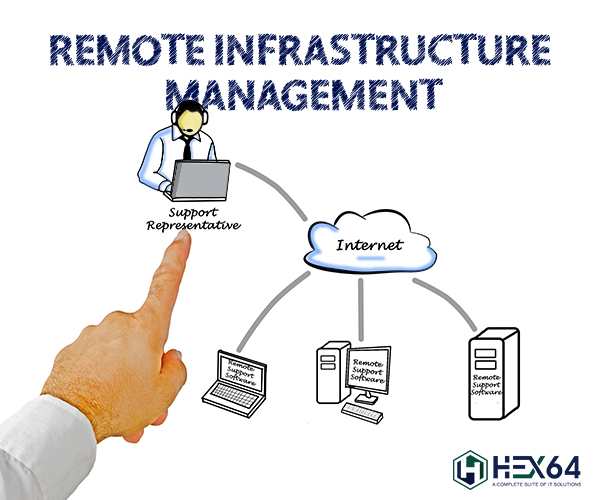
What is RMM (Remote Monitoring And Management)? In essence, it is the method of controlling SMB IT systems such as desktops, laptops, and servers that are on the network and these devices can be managed through...
With the improvement in technologies and change in customer demand, the idea of business expansion has changed. Companies are taking steps to intensify their enterprise practices to meet changing customer requi...
A cybersecurity audit is planned to comprehensively analyze and study your company’s IT infrastructure. It identifies threats and vulnerabilities that highlight vulnerable locations and high-risk performa...
Assume all the problems you face when you try to connect to a network. You may have seen cases where you are making everything right but still helpless to connect. Let’s take another example where ...