Businesses that understand how to prevent a data breach can incur costly penalties, loss of business and destroy their reputation. With more and more collaboration between companies, merchants, suppliers and us...
The world of software development underwent a major change with the emergence of DevOps in 2008. This led to a fundamental shift in focus in the company’s culture, organizational principles, and approach ...
Penetration testing is an effective testing process that helps to uncover the critical security issues of your system to check for exploitable vulnerabilities to their IT Infrastructure, or web applications. ...
Static server room infrastructure will soon be an IT residue. Digitization has accelerated innovation in business infrastructure, heading to the division of devices and applications beyond the IT ecosystem. Whi...
Pegasus is spyware produced by NSO Group, it’s an Israeli surveillance company, that helps spies and spies hack phones. In 2019, the situation came to light when WhatsApp charged the business in a US cour...
Now that the modern workplace becomes more and more sophisticated as it is interconnected, businesses should expect more complex and targeted attacks that threaten an organization’s entire infrastructure ...
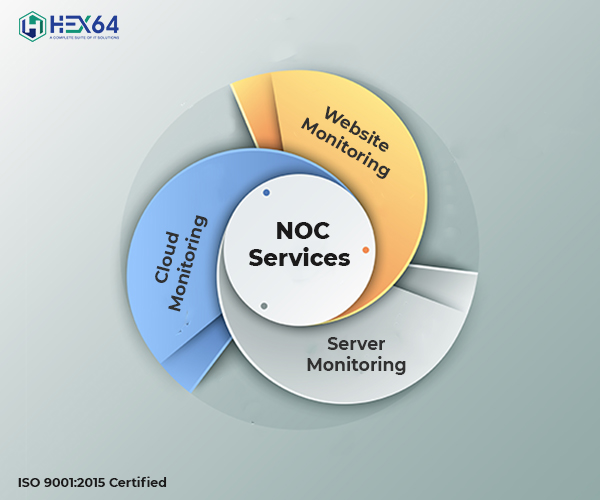
Network operations deal with the activities executed by internal networking teams or third parties that organizations and service providers rely on manage, monitor and respond to alerts on the administration an...
The right network automation platform can help administrators build and maintain an organization network. Find out the top preference in the market and the benefits they offer.The current boom in network automa...
The disputes for and against outsourcing the IT services consumed by a business are several and diverse.One item to recognise is that there is no ‘one measurement fits all’ in this figure. Possibilities are tha...
The digital transformation has dramatically altered the cybersecurity expectations of healthcare offerings as the number of associated devices collapsed and network perimeters began to grow. And, this digital t...